In Windows Djoin, the user can establish a remote and secure connection to a work domain using credentials from the enterprise. The user effectively joins that domain.
Windows Domain join was introduced in Windows 7 and can still work even if there is no immediate connection. The offline Djoin component eases the deployment of desktops in large corporations. In Windows Server 2008 R2, a command called Djoin.exe was introduced so administrators could have an easier time joining desktops to a domain. However, many Windows 7 systems running Windows Server 2008 R2 were unable to join their domain after the Windows Server 2012 release because of the exclusion of offline Djoin from the operating system.
This article explains how offline Domain join works in Windows 7 and then how it works in Windows Server 2012.
Note that this article does not guide for setting up a workgroup configuration on a laptop or any mobile device. It also does not guide Active Directory Domain Services (AD DS) domain controllers or enterprise certificates.
Requirements and Considerations
The following considerations and requirements apply to offline Djoin:
You can only use Windows 7 Enterprise, Windows 7 Ultimate, Windows 8 Pro, or Windows 8 Enterprise editions.
A target computer running any of these operating systems needs to have access to a domain controller in the workgroup (or work organization).
Table of Contents
Join a Computer to a Domain
For Active Directory Federation Services to function, every computer that functions as a federation server must be joined to a domain. federation server proxies may be joined to a domain, but this is not a requirement.
You do not have to enter a Web server to a domain if the Web server is hosting claims-aware applications only.
Membership in Administrators, or equivalent, on the local computer, is the minimum required to complete this procedure. Review facts about using the appropriate accounts & group memberships.
The information on this page is provided for general use in support cases, not as the final word on Djoins. The terms and conditions of Microsoft Services are also applicable to this article.
Planning for Windows Server 2003 Domain Controls.
For performance reasons, use at least a dual-processor computer for each domain controller. The level of performance you get will depend on the following factors:* Number of users and groups in the domain.* Applications that run on the domain controllers.* Size of log files. Each time a user changes his or her password, the system writes a log entry of approximately 20 KB in size to the security event log. After several years, this can amount to several gigabytes of data per domain controller. If you want to conserve disk space or if the security logs are being purged frequently, write access is not required for the following files:* Ntlogmgr.log* Securitymgr.log* Eventquery.vbsAccess is required for the following file, however:* Eventquery. VBS
Membership in Domain Admins, or equivalent, is the minimum required to complete this procedure. To modify objects in Active Directory, you must be a member of the Enterprise Admins group. By default, the Domain Admins group does not include the Enterprise Admins group.
Offline Domain join with DirectAccess policies scenario overview
DirectAccess offline Domain join is a method that computers running Windows Server 2016, Windows Server 2012, Windows 10, and Windows 8 can operate to join a domain without being physically joined to the corporate network, or connected through a VPN. This makes it likely to join computers to a domain from locations where there is no connectivity to a corporate network. Offline Domain join for DirectAccess provide DirectAccess policies to clients to allow remote provisioning.
Employment involves three steps: (1) Server-side provisioning, (2) Client-side provisioning, and (3) Provisioning the domain with a DHCP reservation. The client computer can be a Windows 10 or Windows 8 device or a desktop computer that’s connected to the corporate network through a VPN connection. The client-side process is known as DirectAccess policies deployment. When the user enables or refreshes DirectAccess, the DirectAccess Policies Deployment service starts.
The DirectAccess policies deployment service runs on a computer that has one or more of the following roles: Active Directory Certificate Services and Certificate Templates, Active Directory Certificate Services and Dynamic Access Management, Active Directory Certificate Services and Internet Key Exchange (IKE), Active Directory Certificate Services and Remote Access Service, or Active Directory Certificate Services and Resource Manager.DirectAccess policies deployment involves two steps: (1) Server-side provisioning, and (2) Client-side provisioning.
More detailed information is available in the following article: DirectAccess Offline Domain join with Direct Access Policies.
Windows Domain join is a feature that lets users establish a remote and secure connection to a work domain using credentials from the enterprise, allowing them to effectively “join” that domain. Windows Djoin was introduced in Windows 7 and can still work even if there is no immediate connection.
The offline Djoin feature eases the deployment of desktops in large enterprises. In Windows Server 2008 R2, a command called Djoin.exe was introduced so administrators could have an easier time when remotely deploying computers that are joining a domain. In Windows, 2010 this process was expanded to include the use of Group Policy for computer startup and shutdown in addition to remote user logon provisioning.
Prepare for offline Djoin
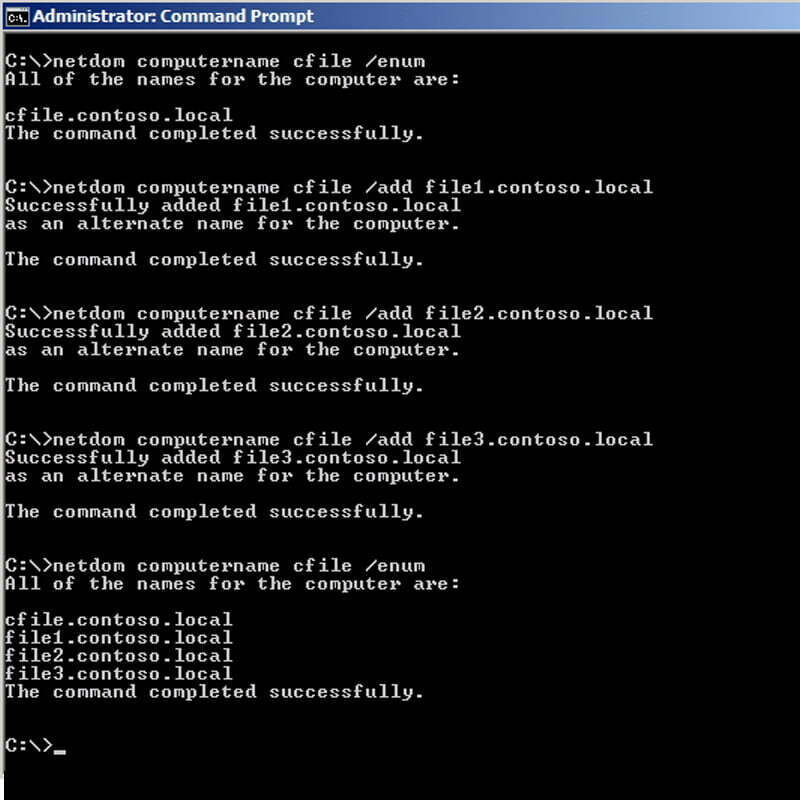
Create the machine account.
Checklist the membership of all security groups to which the machine account belongs.
Gather the needed computer certificates, group policies, and group policy objects to be applied to the new client(s).
Assign the machine account to the appropriate security group.
Make the shortcut that users will use to join a workgroup via the command-line interface (CLI).
Prepare for offline Djoin
To prepare a computer for offline Domain join, you must perform the following steps: Create the machine account. Inventory the membership of all security groups to which the machine account belongs. Gather the required computer certificates, group policies, and group policy objects to be applied to the new client(s). Assign the machine account to the appropriate security group. Create the shortcut that users will use to join a workgroup via the command-line interface (CLI).
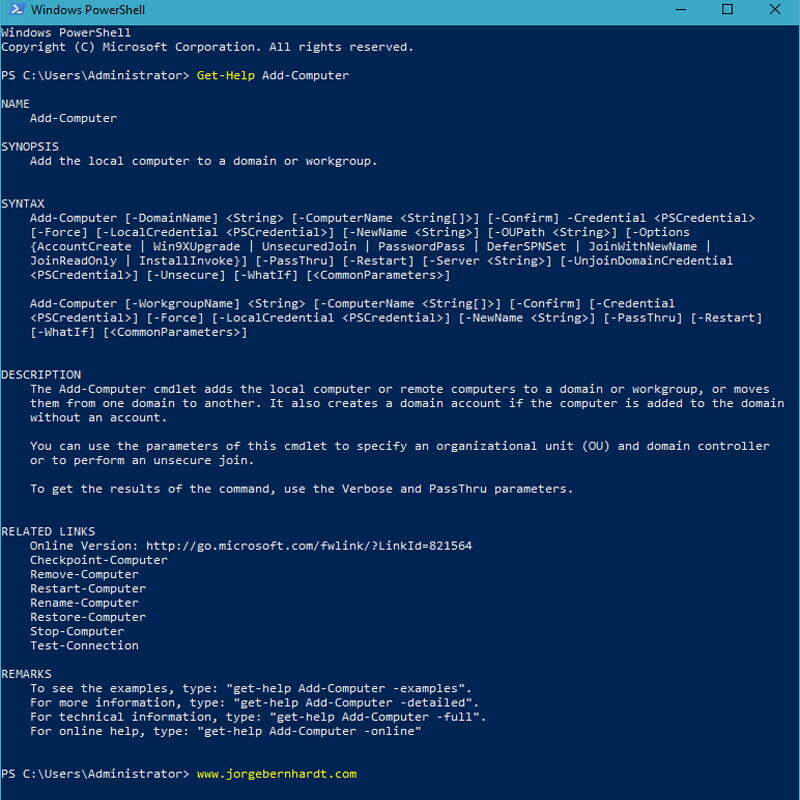
TOC: Windows Server 2008 R2 – Offline Djoin using Djoin.exe
Introduction
Prepare for offline Djoin Use Djoin.exe Prepare for offline Djoin Troubleshooting offline Djoining using Djoin.exe
A common scenario with Windows Server 2008 R2 is deploying many desktops for Djoin. The process of joining a desktop to a domain can be long and sometimes seem to take forever. This blog will show you how you can prepare your environment for offline Djoining, or in other words, having a machine that is not connected to the network obtains its Active Directory Domain Services (AD DS) information from another source and then joining the domain via Djoin.exe.
Operating system requirements
You can run Djoin.exe for DirectAccess only on computers that run Windows Server 2016, Windows Server 2012, or Windows 8. The computer on which you run Djoin.exe to provision computer account data into AD DS must be running Windows Server 2016, Windows 10, Windows Server 2012, or Windows 8.
Only one computer can be specified to run Domain Join.exe at a time. You cannot use Djoin.exe to provision computer account data into AD DS on a remote computer and then again use Djoin.exe to join that computer to an existing domain as part of DirectAccess.
Domain Join.exe can be used only to provision computer account data into AD DS. For example, it cannot be used only to join a domain.
The computer account that is created by using Djoin.exe must be at least Domain computers or Member servers in the domain, but it can also be a Computer object in other domains in the forest or even a Workstations object into which computers are joined.
Djoin.exe can be used only to provision computer account data into AD DS. For example, it cannot be used only to join a domain.
The computer account that is created by using Djoin.exe must be at least Domain computers or Member servers in the domain, but it can also be a Computer object in other domains in the forest or even a Workstations object into which computers are joined.
You must use Djoin.exe from a computer on your corporate network or from the DirectAccess server running on your corporate network.
You must use Djoin.exe from a computer on your corporate network or from the DirectAccess server running on your corporate network.